| This is documentation for Semarchy xDI 5.3 or earlier, which is no longer supported. For more information, see our Global Support and Maintenance Policy. |
Search Guard Security
Overview
Search Guard is a security system that can be used to protect Elasticsearch clusters.
When secured, a cluster requires the use of keystores, truststores, and user / password authentication to be accessed.
This page explains how to work with Search Guard in Semarchy xDI.
| We recommand to learn the basics in Getting Started With Elasticsearch Component before following this page. |
Installation of libraries
The first step is to retrieve and add in your Elasticsearch Module the Search Guard third-party libraries.
Make sure to use the same third-party libraries versions between Search Guard and Elasticsearch
| We cannot provide the exact list of third-party libraries as it depends on the Search Guard and Elasticsearch versions. In most cases, the required third-party libraries can be found in the lib/ folder of the Elasticsearch server installation. |
Below, an example of libraries for the 2.4.1 version of Elasticsearch and Search Guard
apache-log4j-extras-1.2.17.jar
commons-cli-1.3.1.jar
compiler-0.8.13.jar
compress-lzf-1.0.2.jar
elasticsearch-2.4.1.jar
guava-18.0.jar
HdrHistogram-2.1.6.jar
hppc-0.7.1.jar
jackson-core-2.8.1.jar
jackson-dataformat-cbor-2.8.1.jar
jackson-dataformat-smile-2.8.1.jar
jackson-dataformat-yaml-2.8.1.jar
jna-4.1.0.jar
joda-convert-1.2.jar
joda-time-2.9.4.jar
jsr166e-1.1.0.jar
jts-1.13.jar
log4j-1.2.17.jar
lucene-analyzers-common-5.5.2.jar
lucene-backward-codecs-5.5.2.jar
lucene-core-5.5.2.jar
lucene-grouping-5.5.2.jar
lucene-highlighter-5.5.2.jar
lucene-join-5.5.2.jar
lucene-memory-5.5.2.jar
lucene-misc-5.5.2.jar
lucene-queries-5.5.2.jar
lucene-queryparser-5.5.2.jar
lucene-sandbox-5.5.2.jar
lucene-spatial-5.5.2.jar
lucene-spatial3d-5.5.2.jar
lucene-suggest-5.5.2.jar
netty-3.10.6.Final.jar
netty-buffer-4.0.37.Final.jar
netty-codec-4.0.37.Final.jar
netty-common-4.0.37.Final.jar
netty-handler-4.0.37.Final.jar
netty-tcnative-1.1.33.Fork17-linux-x86_64.jar
netty-transport-4.0.37.Final.jar
search-guard-ssl-2.4.1.16.jar
securesm-1.0.jar
snakeyaml-1.15.jar
spatial4j-0.5.jar
t-digest-3.0.jarMetadata Configuration
Overview
Open the Elasticsearch Metadata and configure it as follow.
-
Set the HTTP user and password
-
Set the Path Home
-
Open the Security tab and fill the Security settings
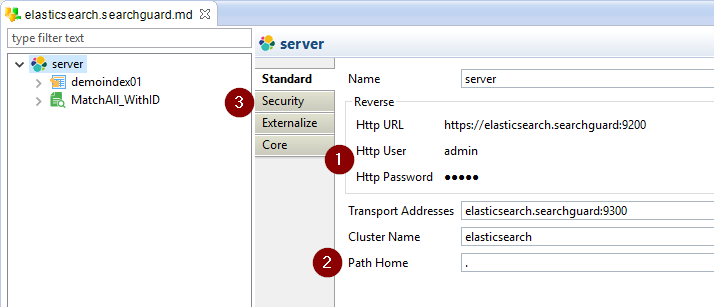
HTTP User and Password
The HTTP user and password will be used when performing reverse operations on the cluster.
This is the login asked when trying to access the cluster from a browser, for instance.
Path Home
The Path Home is the Elasticsearch installation path on the server.
You can use "." to tell the Elasticsearch driver to use the current installation.
Security
The Security settings are defined in Security tab.
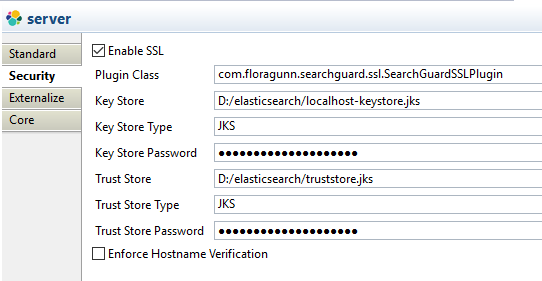
The security settings allow to define the location and properties of the Key Store and Trust Store that will be used by the Runtime when executing Elasticsearch flows.
The Key Store and Trust Store to use are the ones authorized on SearchGuard.
The following propertie are available:
| Property | Description | Example |
|---|---|---|
Enable SSL |
Set it to true to enable the security |
|
Plugin Class |
The Java class to use for security. |
For SearchGuard: |
Key Store |
Location of the Key Store file. The Runtime must be able to access it. |
D:/elasticsearch/localhost-keystore.jks |
Key Store Type |
Key Store Type (JKS or PKCS12) |
JKS |
Key Store Password |
Password of the Key Store file. |
|
Trust Store |
Location of the Trust Store file. The Runtime must be able to access it. |
D:/elasticsearch/truststore.jks |
Trust Store Type |
Trust Store Type (JKS or PKCS12) |
JKS |
Trust Store Password |
Password of the Trust Store file. |
That’s it, Semarchy xDI is now ready to work with Search Guard secured Elasticsearch clusters.
You can design your Mappings and Processes as usual.
The security will be handled by the Metadata and the Runtime.